WASHINGTON, Sept. 13, 2017 - Houston-area flooding in Hurricane Harvey’s wake has been deadly, costly, and persistent. Hurricane Irma is delivering more of the same. But the cumulative damage from these two record-breaking hurricanes could pale in comparison to the impacts of a sudden cyberattack on vital infrastructure resources such as the electric grid, nuclear power plants, oil and gas pipelines and hydropower dams. This type of cyberstrike could come without warning or geographic limits.
The joint U.S.-Israeli attack on Iran’s nuclear development program in 2008 proved that destruction is possible. The attack’s Stuxnet software infiltrated the control systems for Iran’s main nuclear enrichment facility and destroyed a fifth of Iran’s centrifuges.
Recognizing current cyberthreats, President Trump signed his Executive Order on “Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure” in May to guard against “catastrophic regional or national effects on public health or safety, economic security, or national security.”
The risks of cyberattacks were highlighted again last week when Symantec released a startling warning about Dragonfly 2.0 attacks focused on U.S. energy infrastructure. “Dragonfly is a highly focused group, carrying out targeted attacks on energy sector targets since at least 2011, with a renewed ramping up of activity observed in the last year,” Symantec warned. It noted that “Sabotage attacks are typically preceded by an intelligence-gathering phase where attackers collect information about target networks and systems and acquire credentials that will be used in later campaigns.”
Congress is also paying attention. In a series of hearings, Senate Energy Committee Chair Lisa Murkowski, R-Alaska, has warned that “This is not the time for the United States to rest on the question of cybersecurity. The number, scope, and severity of attacks continue to increase, and we must press government to be of greater assistance to assist owners and encourage better equipment designs.”
 Washington Democrat Maria Cantwell, the committee's ranking member, is equally concerned, warning that “The United States must prioritize the protection of our critical energy infrastructure. We cannot wait before we have a large-scale attack before we act.”
Washington Democrat Maria Cantwell, the committee's ranking member, is equally concerned, warning that “The United States must prioritize the protection of our critical energy infrastructure. We cannot wait before we have a large-scale attack before we act.”
Further warning comes from the U.S. Securities and Exchange Commission, which issued a risk alert in August that “cybersecurity remains one of the top compliance risks for financial firms.”
Another wake-up call comes from last week’s belated announcement from credit monitoring company Equifax that hackers obtained Social Security numbers and other data for about 143 million U.S. consumers.
The breach took place from May to July this year and was discovered by Equifax on July 29 when it “acted immediately to stop the intrusion.” So the hackers had from one to four months to make use of the stolen information for identity theft before Equifax reported the attack publicly Sept. 7. (To find out if your personal information was stolen, go to Equifax’s Cybersecurity Incident page or phone 866-447-7559.)
Equifax CEO Richard Smith acknowledged the need for even a highly security-conscious company like his to improve its cyberdefenses. He explained that “Confronting cybersecurity risks is a daily fight. While we’ve made significant investments in data security, we recognize we must do more. And we will.”
What compounds the threat to the nation’s critical infrastructure is the fact that an estimated 85 percent of key facilities like power plants and pipelines are privately owned. This means that while the federal government houses the legal authority, expertise, and classified intelligence needed to combat cyberattacks, these federal resources need to be shared with and acted on by the private companies that now are the front line in today’s cyberwarfare.
To bridge the public/private gap, one urgent recommendation from the private sector is to “deputize” business leaders so that they can access highly confidential threat and countermeasures intelligence instantly. Needed information is available at the federal level, thanks to existing programs such as the Department of Energy’s Cybersecurity Risk Information Sharing Program (CRISP), operated by the Electricity Information Sharing and Analysis Center (E-ISAC). This program to provide “bi-directional cyberrisk information sharing” uses classified analysis of network traffic to identify attacks. The challenge is finding ways to share this intelligence instantly with private companies without compromising classified systems.
Congress authorized public/private sharing in the Cybersecurity Act of 2015, signed into law by President Obama. But experts say far more needs to be done to implement effective real-time sharing.
Eversheds Sutherland attorney Michael Bahar, former deputy legal advisor to the National Security Council and former minority staff director and general counsel for the U.S. House Intelligence Committee, was lead drafter and negotiator for 2015’s Cybersecurity Act as part of his House Intelligence Committee work.
Now as the U.S. leader of Eversheds Sutherland’s global cybersecurity and privacy team, Bahar tells Agri-Pulse that combating cyberthreats is so critically urgent that since neither government nor the private sector “can do it alone,” both have “indispensable roles to play.” In one of the ongoing congressional hearings on cybersecurity, retired Gen. Keith Alexander, former Director of the National Security Agency and CEO of IronNet Cybersecurity, warned that “private-sector entities cannot practically be expected to defend themselves against nation-state attacks in cyberspace.”

Eversheds Sutherland Partner Michael Bahar
“We are very vulnerable,” Bahar explains. “Some sectors have done a really good job in shoring up their cybersecurity, mostly because they were already the victims of serious breaches. What’s most troubling to me is that while the industries that have been attacked have done a lot to improve their cybersecurity, those industries that have not yet been fully attacked . . . remain among the most vulnerable.”
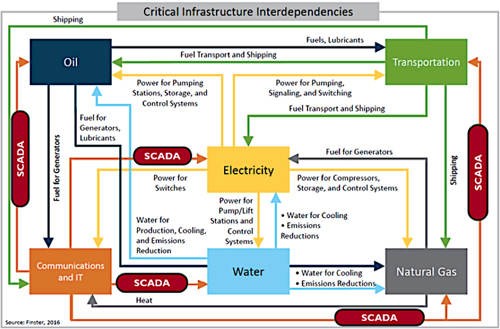
Bahar points out that “most critical infrastructure is run from what are called industrial control systems” that originally were designed “to be air gapped, meaning not connected to the Internet.” He says that as today’s control systems are updated, true air gaps are disappearing, leaving more facilities vulnerable to hackers accessing control systems through the Internet. He says Symantec’s Dragonfly announcement highlights the fact that “Certain sophisticated nation-state actors have figured out how to jump from IT systems to operational control systems.”
Bahar adds that “the more connected we are, the more vulnerable we become.” He says one problem across industries is that software providers focus on sales, not cybersecurity. “We still allow software to be designed . . . to be first to market,” he says, “with no incentives or sufficient requirements to be secure.”
Along with new software standards, Bahar calls for enhanced deterrence custom-tailored to each adversary and its specific motives such as “undermining elections and democracy,” “industrial espionage,” or “political retribution.” In each case, he says, cyber adversaries “need to know – and internalize – that there will be a cost to any malicious cyber activity.”
Bahar concludes that Dragonfly 2.0 is a major threat because it is “targeting the energy sector” and “preparing the ground for a potential attack.” He says that while even widespread hurricane damage may still be localized compared with a potential cyberattack, “A determined cyber actor who has been proficient in laying the groundwork for an attack, could create simultaneous attacks across the country.”
|
National Infrastructure Advisory Council’s Securing Cyber Assets report, August 2017: “As a nation, we need to move past simply studying our cybersecurity challenges and begin taking meaningful steps to improve our cybersecurity to prevent a major debilitating cyber attack. . . . The National Security Council (NSC) tasked the NIAC to assess how existing federal authorities and capabilities could be employed to assist and better support the cybersecurity of critical infrastructure assets that are at greatest risk of a cyber attack that could reasonably result in catastrophic regional or national effects on public health or safety, economic security, or national security.” |
Read the 45-page National Infrastructure Advisory Council’s Securing Cyber Assets report released Aug. 15, 2017.
For more on U.S. energy infrastructure, read about “the nation’s neglected infrastructure."
#30
For more news, go to www.Agri-Pulse.com


